PROGRAMMING 101: KA-BOOM!! |
||
|---|---|---|
| Fire Support | ||
| CLASS: Anti-Program | COST: 1,120eb | |
| STRENGTH: 3 | MU: 4 | |
| PROGRAMMING: 168 | DIFFICULTY: 28 | |
| FUNCTION(S): Anti-Program | ||
| OPTION(S): Superrealistic ICON | ||
| ICON: A battery of three 240mm howitzers | ||
| DATA: In a bind? That Anti-Personnel program about to flatline you? Not to worry, just call in some fire support. Go ahead. The other ‘runners are doin’ it. So should you! This program enters the main processing module of the target and enters error statements into the routine. | ||
| Sniper | ||
| CLASS: Compiler | COST: 1,400eb | |
| STRENGTH: 6 | MU: 5 | |
| PROGRAMMING: 210 | DIFFICULTY: 35 | |
| FUNCTION(S): Compiler [Demon] Continue reading “PROGRAMMING 101: KA-BOOM!!” | ||
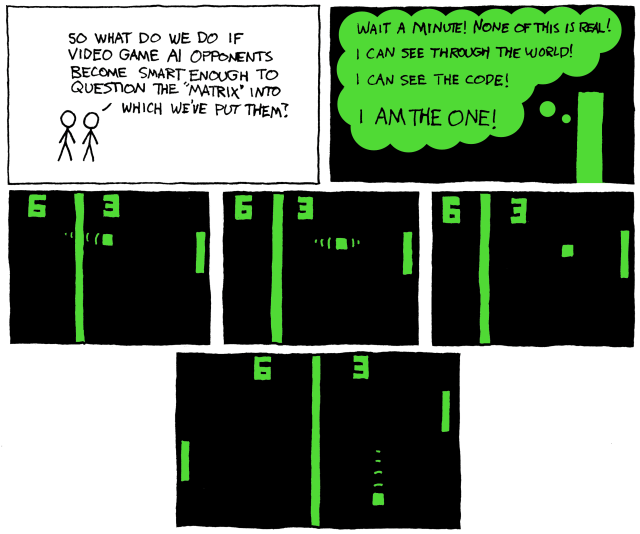
Tag: matrix
Cyberpunk Tech 7
 In my little series of Cybepunk tech allready available today: The brain-computer interface. The very core of every cyberpunk book – the ability to plug yourself into the matrix.
In my little series of Cybepunk tech allready available today: The brain-computer interface. The very core of every cyberpunk book – the ability to plug yourself into the matrix.
Well, today you can use it to surf Second Life. Second life is NOT the virtual reality I imagined reading Neuromancer, but some like it there:
All a user has to do to control his/her avatar is imagine performing various movements. The activity monitored by the headpiece is read and plotted by an electroencephalogram, which relays it to a computer running a brain wave analysis algorithm that interprets the imagined movements. A keyboard emulator then translates the data into signals which can be used to control the movements of the user’s on-screen avatar in real-time.
As usual, boing-boing has the details (including a link to a video)
Botnet Storm punishes its enemies
The first evil computer program that defends itself. Its so cool!
The worm can figure out which users are trying to probe its command-and-control servers, and it retaliates by launching DDoS attacks against them, shutting down their Internet access for days, says Josh Korman, host-protection architect for IBM/ISS, who led a session on network threats.
As you try to investigate [Storm], it knows, and it punishes, he says. It fights back.
As a result, researchers who have managed to glean facts about the worm are reluctant to publish their findings. They’re afraid. I’ve never seen this before, Korman says. They find these things but never say anything about them.
And not without good reason, he says. Some who have managed to reverse engineer Storm in an effort to figure out how to thwart it have suffered DDoS attacks that have knocked them off the Internet for days, he says.
As researchers test their versions of Storm by connecting to Storm command-and-control servers, the servers seem to recognize these attempts as threatening. Then either the worm itself or the people behind it seem to knock them off the Internet by flooding them with traffic from Storm’s botnet, Korman says.
Source: Networkworld